From Zero to Hero: Phishing Campaign. Part 3

See also:
Part 1
Part 2
Chapter 4: Results
The phishing campaign presented in this article lasted one day. The attacked employees of the organization are IT specialists from the development and administration departments - 42 people. The target organization participates in training on countering phishing attacks.
Events since the start of the attack:
00:00: mailing start - 42 emails successfully delivered;
00:30: the first clicks on the links were recorded;
00:40: first successful capture of an authorization session (administrator);
- - - lots of link clicks and two more captured sessions - - -
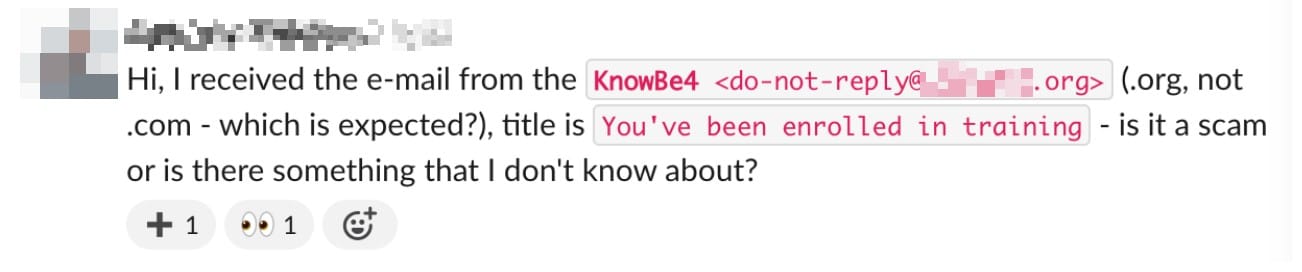
19:05: A message was fixed in the corporate messenger:
21:15: initiated re-sending of the letter;
- - - a lot of link clicks - - -
23:55: employees are notified of a phishing attack in corporate messenger, and the organization's administrators block the phishing email domain.
Recorded results
In my opinion, the attack was successful for the potential attacker.
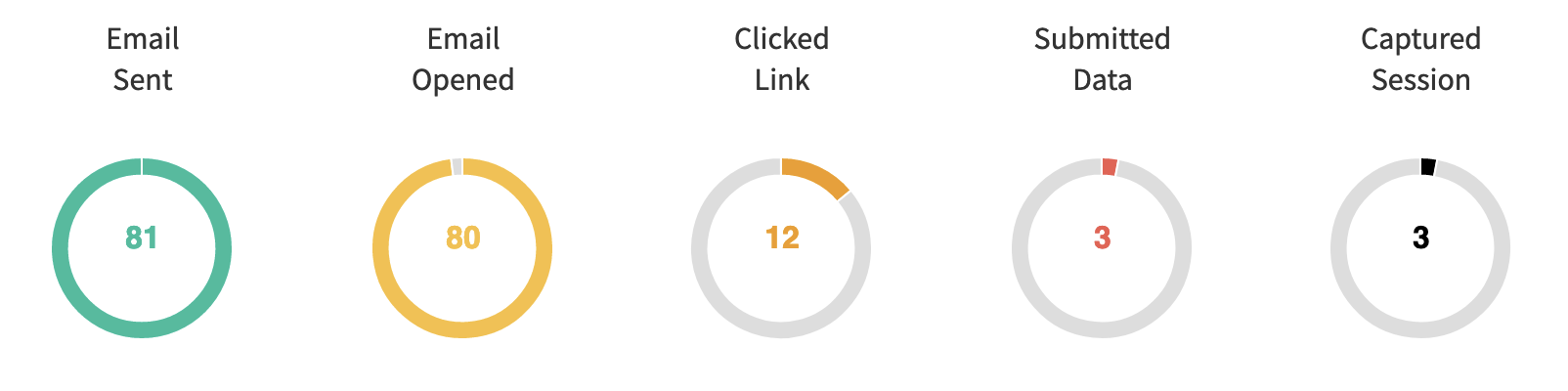
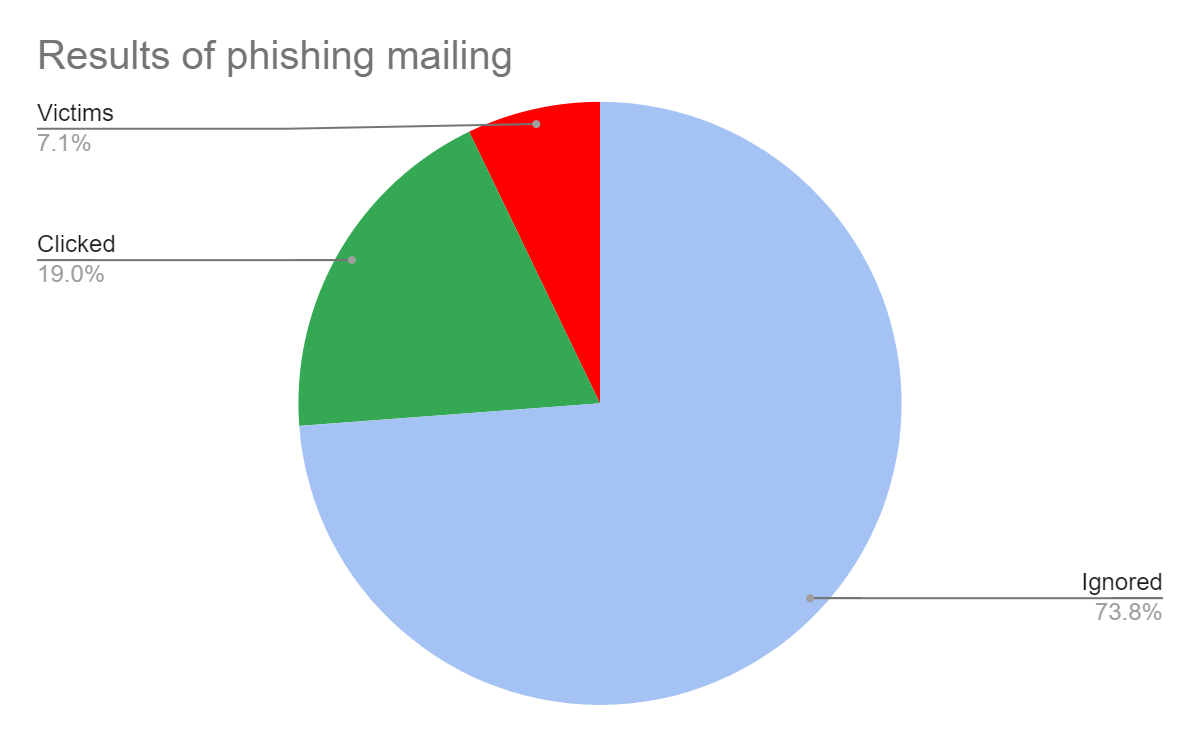
As you can see in the figure, about ¾ of employees simply ignored the emails. It would seem that this is not bad - in my experience, on average, 25% to 35% of recipients react to phishing emails - it would seem that the result is closer to the minimum. However, let's not forget that these are developers and administrators, IT experts, who should be expected to be more attentive and aware of the risks.
Twelve people (19%) clicked on the link, and a quarter of them left their authorization details on the phishing page.
Successfully captured three user sessions with confirmed 2FA (including those with the rights of an organization administrator), allowing access to internal services of the customer's organization: mail, development resources, IT infrastructure monitoring, and administration systems.
It is difficult to overestimate the damage that could have been caused if real hackers had organized the phishing attack. At the same time, the financial cost of the attack amounted to $19 (domain name rent). At this cost, it is obvious that phishing is a real gold mine for various cyber criminals, and the current growth of this type of attack will only gain momentum.
These results show the high efficiency of the techniques presented in this article and the need to implement methods to counteract them. It is also important to note the ineffectiveness of multifactor authorization via TOTP codes and push notifications. The use of multifactor authorization creates an illusion of security in the context of phishing attacks, putting the vigilance of employees (including, as we have seen, those who are supposed to be responsible for the secure environment in the organization) to sleep.
Chapter 5: Recommendations
Recommendations on risk mitigation
- Conduct regular cybersecurity training so employees can recognize the flags of phishing emails;
- Assign users only the access rights they need to do their jobs. This will help mitigate damage in the event of a successful phishing attack;
- Develop and implement a phishing attack contingency plan to respond quickly and minimize damage. Include notification and investigation procedures.
Recommendations to counter
Implementing hardware (CTAP) and passkey solutions can help counteract this type of phishing. These methods are effective because the token/key is tied to the authorization domain, and it is technically impossible to authenticate through a third-party (phishing) domain.
Author: @resource_not_found